Curated, Not Aggregated
AI-powered filtering across 1000+ security news sources. Every article scored for relevance. We cut the noise so you don’t have to.
ThreatNoir is a daily-updated security intelligence platform with curated articles, real-time IOCs, podcasts, and weekly briefs for SOC analysts, security leaders, and engineers.
Your daily security briefing in under 5 minutes. We score every story for relevance, link back to the original source, and keep your signal clean.
Get the daily brief. Free during beta.
No spam. Unsubscribe anytime.
New episodes daily at 07:00 and 16:00 UTC.
Today at a glance
🔥 Supply chain attacks evolved with wormable npm malware targeting developer toolchains 🛡️ Cisco firewalls compromised with persistent bac…
Who it's for
Pick your role to see what ThreatNoir gives you today.
Your morning briefing in 5 minutes. IOCs in your Claude workflow. Focus items tell you what to prioritize today.
The weekly brief your board will actually read. Regulation-aware. Awareness Lessons to share with your team.
Learn security by what is actually happening right now. Root-cause takeaways from real incidents.
IOCs in your MCP server. Webhooks for your security tooling. APIs to automate lookups.
Command center
ThreatNoir is designed to compress the threat landscape into something you can act on—fast.
AI-powered filtering across 1000+ security news sources. Every article scored for relevance. We cut the noise so you don’t have to.
Every story traces back to the original source. IoCs extracted and attributed. Regulation and jurisdiction tagged for compliance teams.
Subscribe to the topics you care about. Get notified via email, Discord, Telegram, or webhook. Only what matters to you.
The easiest way to stay security-aware. Morning and afternoon conversational briefings. Five minutes to know what matters. Listen while you commute.

A longer daily briefing with deeper coverage, additional stories, and more context for security teams.
Latest intelligence
A live sample of what's landing in the archive right now.

CYBERA's H2 2025 report reveals that money mule accounts—the financial exit points for scams—are the most stable and actionable target for fraud prevention. By using agentic personas to directly engage scammers and extract verified account intelligence before transactions occur, CYBERA identified over 16,000 confirmed mule accounts across 72 countries, with 28% remaining active 30+ days after detection, indicating systemic gaps in detection. Regulatory pressure is mounting globally as the UK mandates APP fraud reimbursement and the US, Canada, and Australia follow suit, making proactive mule account intelligence a critical defense lever.
Researchers used AI to identify 38 security vulnerabilities in OpenEMR, an open-source electronic health record (EHR) platform deployed across more than 100,000 healthcare providers worldwide. The flaws span database compromise, remote code execution, and data theft capabilities, exposing sensitive patient health information to potential attack. This discovery highlights both the security risks in widely-used healthcare infrastructure and the emerging role of AI in vulnerability detection.

Ukrainian authorities arrested three individuals (aged 19, 21, 22) who compromised over 610,000 Roblox gaming accounts between October 2025 and January 2026, generating $225,000 in profit. The threat group distributed info-stealing malware disguised as a game-enhancer tool to harvest login credentials, then categorized and sold accounts—including at least 357 high-value "elite" accounts—via Russian websites and closed online communities. The suspects face charges under theft and unauthorized IT system interference statutes, with sentences up to 15 years.

Offshore.LC is a bulletproof hosting provider operating across six jurisdictions (NL, RO, RU, UA, SE, FI) offering dedicated servers, VPS, and RDP with explicit DMCA non-responsiveness, zero-log policies, and crypto-only payments. The service markets itself as takedown-resistant infrastructure designed for threat actors, with anonymous signup, no KYC requirements, and full root access. This represents active criminal infrastructure-as-a-service targeting malicious actors.
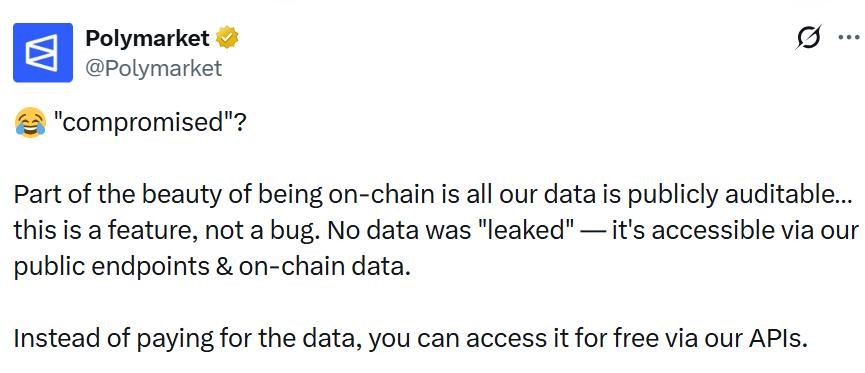
A threat actor using the alias "Xorcat" claims to have breached Polymarket, a decentralized cryptocurrency prediction market, by exploiting multiple API vulnerabilities including undocumented endpoints, pagination bypass, CORS misconfiguration, and two publicly disclosed CVEs (CVE-2025-62718 and CVE-2024-51479). Polymarket denies the breach, asserting that most exposed data is already public on the blockchain and that the incident is likely data scraping rather than a true breach. Security researchers agree the evidence points to automated data harvesting rather than unauthorized system access.

A critical authentication bypass vulnerability affecting cPanel and WebHost Manager (WHM) was patched in an emergency update across multiple product versions (11.110.0.97, 11.118.0.63, 11.126.0.54, 11.132.0.29, 11.136.0.5, 11.134.0.20). The flaw allows unauthenticated attackers to gain unauthorized access to the control panel, potentially compromising hosted websites, databases, and email. Namecheap temporarily blocked access to ports 2083 and 2087 to protect customers until patches became available.
Awareness Lessons
Root-cause takeaways extracted from the latest incidents—10× faster to internalize than a full write-up.
CVE-2026-41651 demonstrates how a Time-of-Check-Time-of-Use (TOCTOU) race condition in PackageKit allowed unprivileged users to gain root access and install arbitrary packages without authentication. This vulnerability existed undetected for approximately 14 years across major Linux distributions, affecting millions of systems worldwide. The flaw's longevity underscores the critical importance of proactive vulnerability scanning and timely patch management, as attackers could have exploited this weakness to completely compromise affected systems.
The Vidar infostealer campaign demonstrates how attackers combine social engineering tactics with advanced evasion techniques to bypass security controls. By using fake CAPTCHA prompts and compromised GitHub repositories, attackers trick users into executing malicious code that appears legitimate. The malware's use of steganography to hide payloads in image files and fileless execution through trusted Windows binaries shows how proper system hardening and user education are critical defensive layers. This attack highlights the importance of both technical controls and human awareness in preventing sophisticated malware infections.
UNC6692 successfully combined email bombing with Microsoft Teams impersonation to trick victims into executing malicious Snow malware, which then established persistent access and enabled credential theft. The attack exploited human trust in IT support communications and leveraged legitimate cloud platforms to bypass technical defenses. This demonstrates how sophisticated social engineering can override security controls when users lack proper awareness training and verification procedures for IT support requests.
Integrate IOCs into your AI workflow
Search and query threat indicators directly from Claude Code, VS Code, or any MCP-compatible client.
{
"mcpServers": {
"threatnoir-iocs": {
"command": "npx",
"args": ["threatnoir-mcp-iocs"],
"env": { "THREATNOIR_API_KEY": "your-key-here" }
}
}
}Tip: store your key as an environment variable — you can generate one in Settings → API Keys.
Pricing
Early users get grandfathered pricing when Pro launches. We will never charge existing users retroactively.
Everything, during beta
Coming soon for power users
For security teams and enterprise
Free account
Sign in to tailor delivery channels, manage alert topics, and generate API keys for developer access.
Most content is free without signing up.
Personalized alerting
Subscribe for personalized security intelligence delivered to your preferred channel.
Subscribe
Enter your email to configure alerts.